Just recently, Google released an update for its browser Google Chrome, which aims to fix 14 security flaws, including one “zero-day” flaw that’s already being actively exploited by an unknown group of hackers. As such, both the tech giant as well as many tech. experts on the Internet recommend that all Chrome users apply that same browser update as soon as possible.
The reason being is that if that same zero-day security flaw is left unchecked, that could very well leave a user’s system extremely vulnerable to attacks. In fact, Google itself ended up classifying these required fixes that came with its latest Chrome update as being critical, high, and of medium importance.
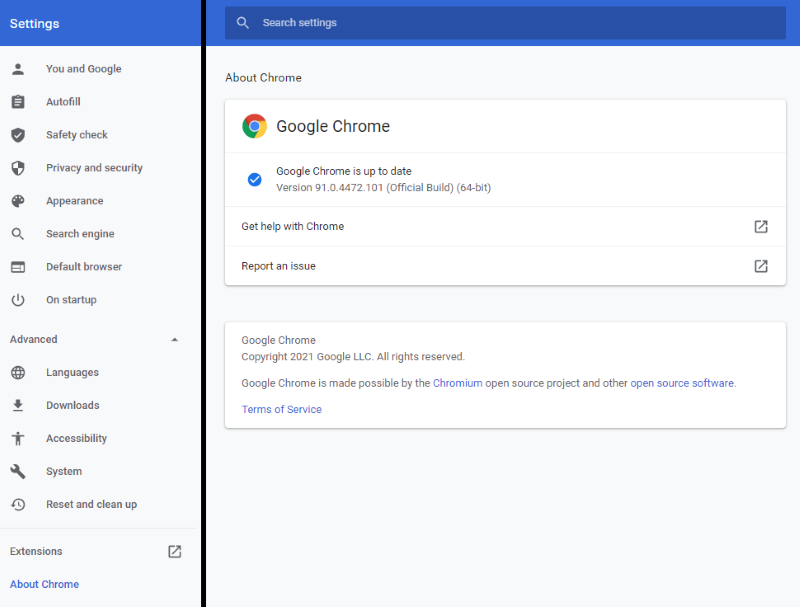
With all that said, both Windows and Mac users that surf the internet by using Google’s famous Chrome browser will immediately want to ensure that they’re running Chrome on its latest 91.0.4472.101 version.
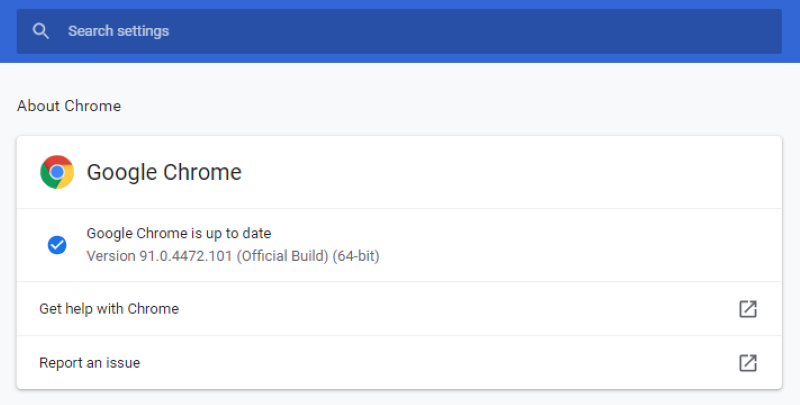
So, in order to make sure that you’re already running Chrome on its latest build, just launch the browser and then click on the three vertical dots that can be found at the top right of the browser window. Then, simply scroll down and click the Settings Button, and then click on the “About Google Chrome” button that’s found at the very bottom of this left column menu.
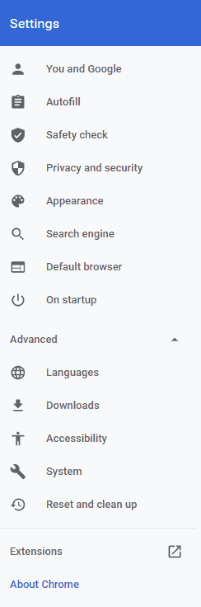
From there, a new fly-out menu window will open up, where you’ll then be able to view your Chrome browser’s current version number, as well as to update the browser in the case that it wasn’t automatically updated in the background for you. In other words, if this fly-out menu window tells you that your browser is up-to-date, you’re basically done. Otherwise, it will automatically start downloading Chrome’s new 91.0.4472.101 version, after which you simply have to relaunch the browser to have it applied.
Nevertheless, for any Chrome user that doesn’t immediately update their browser, know that Google also stated on its recent official blog post announcement that the company should also be pushing out the update to the remaining users within the upcoming days or weeks.
On an additionally side note that’s meant specifically for Linux users, know that you may have to wait for your Chrome’s newer version to be rolled out at a later date.
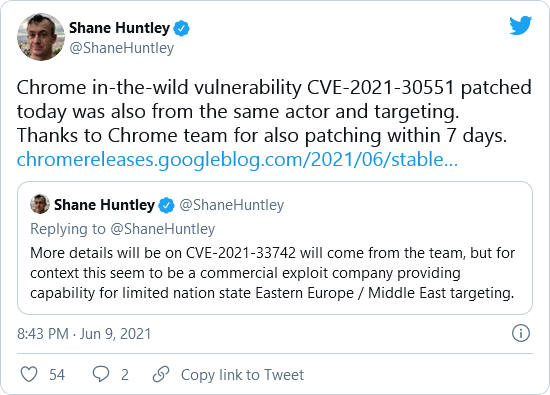
Now, note that Google Chrome’s recent zero-day security flaw, which was catalogued by Google as CVE-2021-30551, is directly related to a Windows 10 flaw, which, somewhat ironically, was also a zero-day flaw (labelled as CVE-2021-33742), which was actually discovered just last week by Google researchers, and then patched on June 8th, 2021 by Microsoft.
This direct-correlation between the two different zero-day flaws from Chrome and Windows 10 was pointed out on a Twitter post made by none other than director of Google’s Threat Analysis Group, Shane Huntley, who declared that “Chrome in-the-wild vulnerability CVE-2021-30551 patched today was also from the same actor and targeting,” stating that attackers who exploited that vulnerability also took advantage of the vulnerability from the just previously fixed Windows 10 CVE-2021-33742 zero-day flaw.
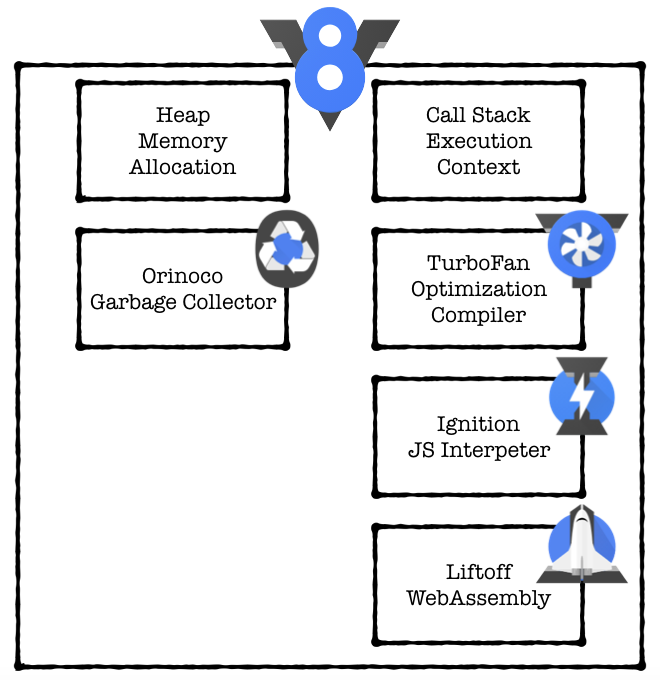
In its official update release note of the latest Chrome update (version 91.0.4472.101), Google described its browser’s latest CVE-2021-30551 security flaw as due to “type confusion in V8,” which was reported by Clément Lecigne, who’s part of Google’s Threat Analysis Group, and this was also equally reported by security researcher Sergei Glazunov of Google Project Zero.
For those less tech-savvy, note that V8 is the open-source high-performance JavaScript rendering engine used by Chrome, as well as by many other competing browsers that are also based on the Chromium project, which would include Microsoft Edge, Opera, Brave and Vivaldi.
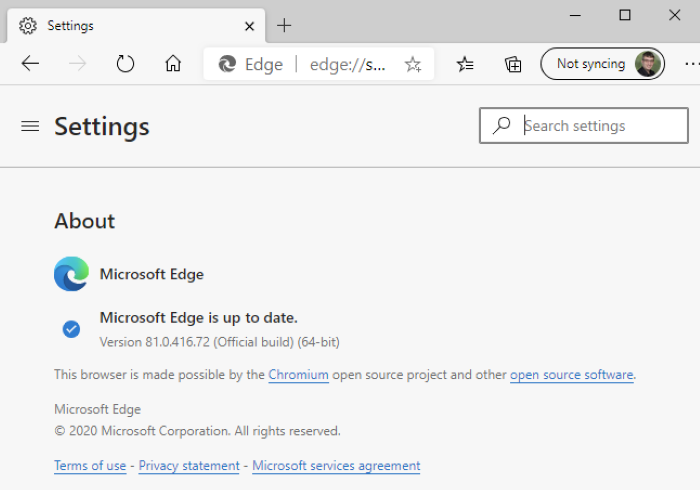
As such, even if you’re not using Google Chrome, you’ll still want to make sure that you’re running the latest version for whichever one of those Chromium project-based browsers you prefer to use. That said, keep in mind that most of those browsers that use Chromium for rendering will also list their current Chromium version number, for which users should then diligently check in order verify if a patch is already available for the browser of their choice.
As an example, if you’re a Microsoft Edge user, all you have to do is to launch your browser, and navigate to the About page, which is exactly where you’ll be able to your browser’s current version number along with an option that allows you to update it the latest version if your Microsoft Edge browser still isn’t on its most current available release.
Other than Chrome and Microsoft Edge, for all the remaining Chromium project-based browsers like Opera, Brave, and Vivaldi, users can also follow a very similar procedure to have their preferred choice of browser updated to its respective latest available release.
On a final note, according to recent post from Tech News website Bleeping Computer, this is already the sixth zero-day flaw exploit for Chrome that occurred just in 2021.





