In computer security, vulnerabilities are weaknesses that can be exploited by a threat actor, such as an attacker, to perform unauthorized actions within a computer system. To exploit a vulnerability, an attacker must have at least one applicable tool or technique that can connect to a system’s weakness. Linux Sudo Command Vulnerability
If you’re familiar with Linux’s command line or any Unix-based platform like macOS, you probably already know what the “sudo” command is used for. This worldwide known command lets you run tasks with admin permissions/higher access levels, which you wouldn’t have without using it.
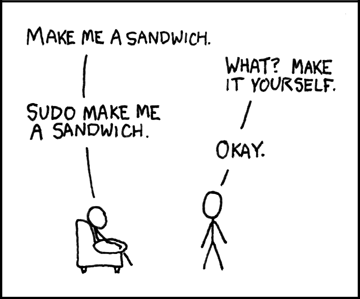
While the command is indeed powerful, recent reports state that maybe it was actually a little bit too powerful. Well, until now that is. Developers have recently confirmed that they finally fixed a major flaw that revolved around the use of the “sudo” command. The command would let malicious users claim root-level access, even if the system’s configuration explicitly forbid it. This means that if an intruder/hacker had just enough access to run the sudo command, the person behind the attack could then perform any action they wanted on a given machine.
The exploit was directly related with sudo’s treatment of user IDs. By typing the command with a user ID of -1 or its unsigned equivalent 4294967295, the system would suddenly see you as if you had root access (user ID 0), regardless of actually recording the actual user ID in its log. And even worst, since the user IDs in question are non-existent in the password database, this basically means that the command wouldn’t require a password to be used.
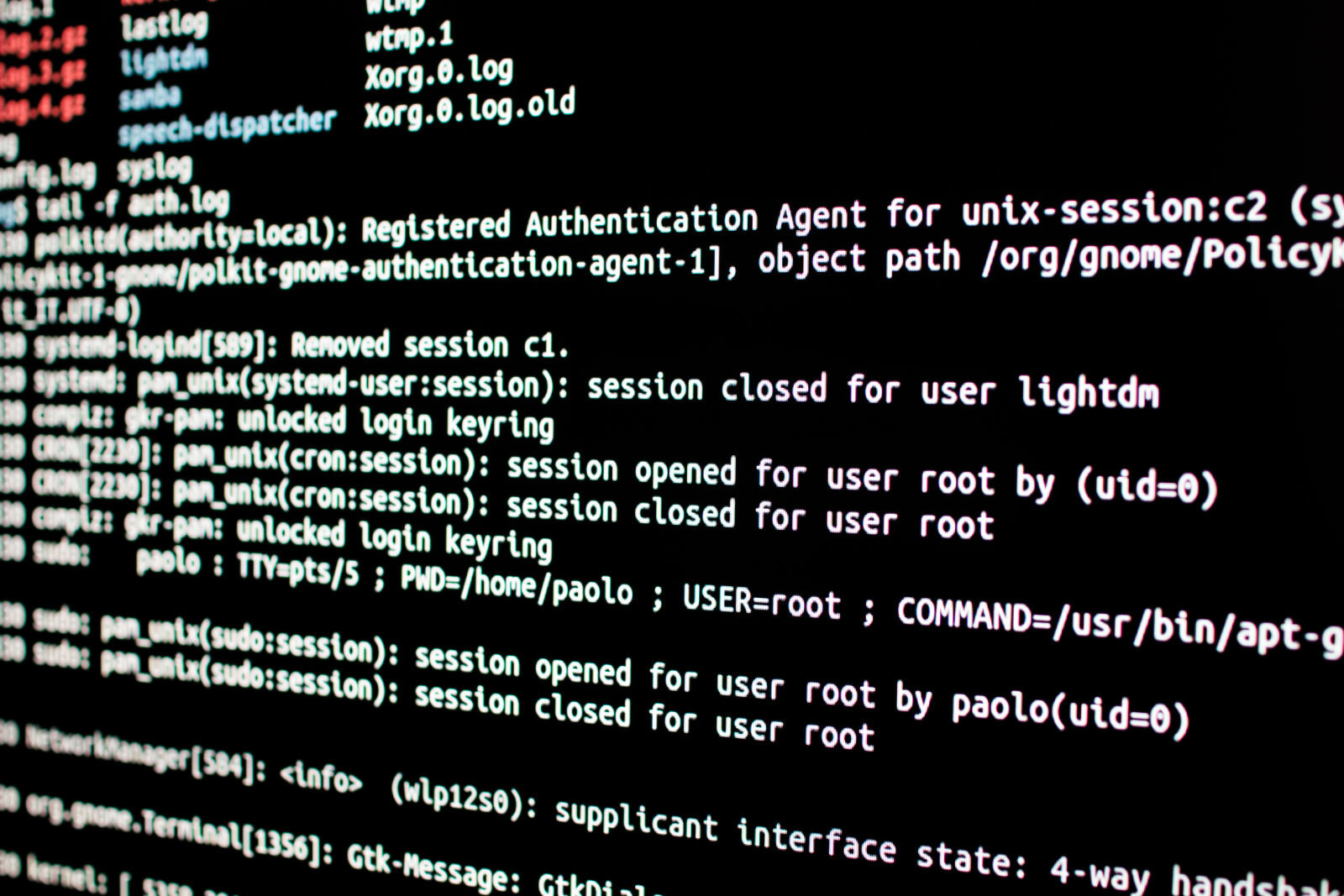
But in case you’re a Linux user, there’s absolutely no reason to be scared about your system’s safety. As stated before, developers already worked on a fix. As a work-around, all you have to do to prevent the exploit via said flaw is to update your system to a newer sudo package (1.8.28 or later).
While you might not be immediately vulnerable, as any system intruder/malicious user will need access to the command line control over your system before they can even consider exploiting the flaw, it isn’t very comforting to know that such an important command was vulnerable.
Once again, remembered to run the update for the newer sudo package (1.8.28 or later) to prevent the flaw from getting exploited on your system.
Also Read: Dr.Duino is an Arduino Uno Starter Kit that’ll help you Master all Arduino Projects





